Vulnerable Exchange Servers
In the wake of the Exchange Zero-day vulnerabilities, Advanced Data was concerned about how many vulnerable servers were left in our region. We pulled the blocks of IP addresses that are used in our region by businesses and entered them into NMap as target IPs. We then leveraged an NMap script released by Microsoft to check if the targets were vulnerable.
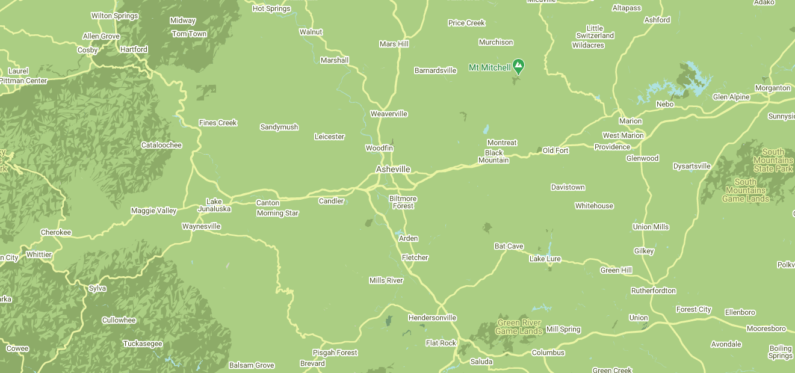
In total we checked about 250,000 IPs which cover Western North Carolina as well as Morganton, Hickory and Greenville/Spartanburg South Carolina. We found 41 Exchange Servers that still had the vulnerability.
For businesses inside our service footprint we contacted them personally to make them aware of the attack. It was simply a courtesy call to notify their IT team that they needed update their email Exchange Server.
Take Aways from The Zero-day Scan
- I was pleasantly surprised there were only 41 remaining, I expected more. This either shows that IT teams are doing their jobs, or that there are active and updated IPS capable firewalls in front of those servers. Either way that’s a good thing.
- Unfortunately this doesn’t tell us how many servers were compromised, just how many were potential targets at the time of the scan. As we discovered, some servers were hacked before the weaknesses were made public. Patching after the hack doesn’t remove the threat once the criminals have gotten in.
- Law firms were highly represented. Not sure why that is.
- There were 4 IT companies (MSPs) on the list! I’m hoping they were honey pots, but evidence wasn’t in their favor!
- People were gracious for the warning and no one hung up on us! ☺️